Crypto links
- Subscribers
- Post coverage
- ER - engagement ratio
Data loading in progress...
Data loading in progress...
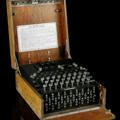
Blunders expose huge cracks in net's trust foundation
U.S. and U.K. spies stole encryption keys from the leading SIM card maker, exposing communications on millions of mobile phones.
Shortly before the release of the 5.8 kernel, a brief patch to a pseudo-random-number generator (PRNG) used by the networking stack was quietly applied to the kernel. As is the norm for such things, the changelog gave no indication that a security vulnerability had been fixed, but that turns out indeed to be the case. The resulting controversy had little to do with the original vulnerability, though, and everything to do with how cryptographic security is managed in the kernel. Figuring prominently in the discussion was the question of whether theoretical security can undermine security in the real world.
The final version of our (@dfaranha @tncardoso @pedroysb @CaioLuders @thotypous) paper about the arbitrary code execution vulnerability in the Brazilian voting machine is finally online. Available free-of-charge from Elsevier for limited time at
https://t.co/eyFyevcSsO.If you have used a private key generated on WalletGenerator.net after August 17, 2018, move your funds immediately to a secure address.
