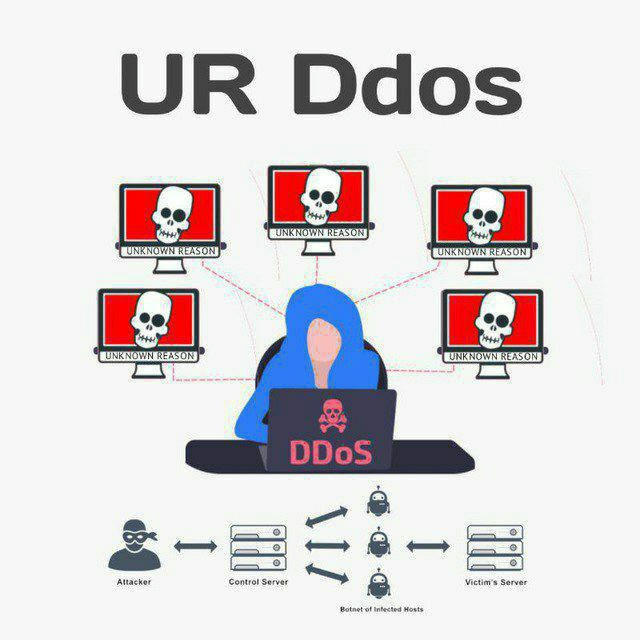
UrDdos
ㅤㅤ (\__/) (•ㅅ•) We are anonymous _ノヽ ノ\_ We are legion / / ⌒Y⌒ Y We do not forgive ( (三ヽ人 / | We do not forget | ノ⌒\  ̄ ̄ヽ ノ Expect us.🎭 ヽ___>、__/ |( 王 ノ〈 (\__/) @UR_DDOS /ミ`ー―彡\ (•ㅅ•) / ╰
Больше2 159
Подписчики
-224 часа
-207 дней
-7930 дней
- Подписчики
- Просмотры постов
- ER - коэффициент вовлеченности
Загрузка данных...
Прирост подписчиков
Загрузка данных...
HTTP 💻 status codes:
These are used in Website Server Development
1xx : Informational ℹ️
- 100: Continue
- 101: Switching Protocols
- 102: Processing
2xx: Success ✅
- 200: OK
- 201: Created
- 202: Accepted
- 203: Non-Authoritative Information
- 204: No Content
- 205: Reset Content
- 206: Partial Content
- 207: Multi-Status
- 208: Already Reported
- 226: IM Used
3xx : Redirection ➡️
- 300: Multiple Choices
- 301: Moved Permanently
- 302: Found
- 303: See Other
- 304: Not Modified
- 305: Use Proxy
- 306: Switch Proxy
- 307: Temporary Redirect
- 308: Permanent Redirect
4xx : Client Error ❌
- 400: Bad Request
- 401: Unauthorized
- 402: Payment Required
- 403: Forbidden
- 404: Not Found
- 405: Method Not Allowed
- 406: Not Acceptable
- 407: Proxy Authentication Required
- 408: Request Timeout
- 411: Length Required
- 412: Precondition Failed
- 413: Payload Too Large
- 414: URI Too Long
- 415: Unsupported Media Type
- 416: Range Not Satisfiable
- 417: Expectation Failed
- 421: Misdirected Request
- 423: Locked
- 424: Failed Dependency
- 425: Too Early
- 429: Too Many Requests
- 431: Request Header Fields Too Large
- 451: Unavailable For Legal Reasons
5xx : Server Error ⚠️
- 500: Internal Server Error
- 501: Not Implemented
- 502: Bad Gateway
- 503: Service Unavailable
- 504: Gateway Timeout
REACTION MUST
❤ 3
9920
Repost from ⏤͟͞𝟒𝟎𝟒 𝐄𝐑𝐑𝐎𝐑 𝐎𝐅𝐅𝐈𝐂𝐈𝐀𝐋⚡
Фото недоступно
Recover by 404 ERROR OFFICIAL⚡
(Recovered) https://indianmerchantnavy.org.in/
(Recovered) https://seasafe.in/
#We_are_indian_hackers
Some bangladesi 2 kodi hackers hacked this site using no redirect vuln hahahahahahah even he didn't uploaded shell i know you don't know how to upload shell nigga come to my dm i will teach you better than yours using no redirect 🤣🤣🤣
#Team404Error
⚡@Team404Error⚡
👍 2🔥 1
11311
Repost from Rajput Haxor Teaching (Haxor1447)
Фото недоступно
Hola amigo 👋😁
This is the last opportunity to grab this live training program of Offensive Pentesting art where you will learn all the things from basic to advanced...
11500
Repost from Rajput Haxor Teaching (Haxor1447)
Syllabus is given here :-
[+] Windows & Linux Exploitation
• FTP Exploitation
• SSH Exploitation
• RDP Exploitation
• WinRM Exploitation
• WebDav Exploitation
• MySQL RCE Exploit
[+] Active Directory
• Active Directory Basic
• AD External Enumeration
• AD Initial Exploitation
• Internal Enumeration/Local Enumeration
• Local & Domain Privilege Escalation
• Lateral Movement & Pivoting
• AD Persistence
• Deligation Attacks
• Capstone Challenge
[+] Windows Privilege Escalation
• Service Exploit
• Registry Exploit
• Access Token Impersonation
• Kernel Exploit
[+] Linux Privilege Escalation
• Kernel Exploit
• SUID/GUID Exploit
• Sudo Abuse
• Cron Jobs
• Weak File Permission
• SSH Key
[+] Memory Corruption Exploit
• Fundamental Understand
• Memory Anatomy
• CPU Register
• CPU Flags
• Stack & Heap
• Buffer Overflow
• Spiking & Fuzzing
• Offset Finding
• Overwriting EIP
• Bad Char Detection
• Getting Right Module
• Shellcode Generation & Execution
[+] Defence Evasion
• Antivirus software Overview
• Detection Methods
• Understanding AMSI
• Bypass AMSI Live
• Antivirus bypass via Thread injection powershell script
[+] Web Application Exploitation
• Web Fundamental
• DNS In detail
• Website Recon
• XSS Attacks
• SQL injection
• Remote Code Execution
• Command Injection
• Local File Inclusion
• Remote File Inclusion
• Broken Authentication/Account Takeover
• Wordpress Exploitation
• Wordpress Username Enumeration
• Wordpress Username Enumeration 2nd method
• Drupal Exploit
Note :- this is just a sample syllabus there are lots many things in live training
13000
Repost from DARK CYBER WARRIOR
Фото недоступно
Bangladesh Biman Bandar Bidyalaya,Jashore Airbase Jashore. Established-1988 has been Hacked by :- DCW
🔓Target : https://bbmb.edu.bd/
🖕Mirror : https://mirror-h.org/zone/5689508/
⚠️Massage -> Stay Away From Indian Cyber Space ⚡
💎 All Indian hackers 💎
#AnonymousIndia #UnknownCyberCult #Indian_Cyber_Punk #TeamNwh #Network_Nine #Black_Dragon_Sec #DarkCyberWarrior #RCF #Demon_Sec #GlorySec #Lapsus #𝐇𝐀𝐂𝐊𝐓𝐈𝐕𝐈𝐒𝐓_𝐕𝐀𝐍𝐆𝐔𝐀𝐑𝐃
🇮🇳 जय हिंद जय भारत हिंदुस्तान जिंदाबाद जय श्री राम 🚩
👍 3🔥 1
14800
RAM BHAKT SENA 🥷🏻🔥❤️🔥 धर्म रक्षा 🚩 JOINED
⚠️I Request All to RETWEET THIS POST BOTH !!
https://x.com/Rambhakhtsena/status/1803082668026040778?t=Z4P6Z_UVgIpICfnnP1-0Ew&s=09
https://x.com/HacktivistVan/status/1803068387196633156
!! tag
KolkataPolice @KPCentralDiv
@WBPolice @DCCyberKP @DCPEastKP @KPSoutheastDiv @KPTrafficDept @Nikhilsingh21_ @HacktivistVan @DCCCyberKP
@randomsena
arrrest Sahil as soon as We have high hope From @KolkataPolice200
Фото недоступно
High Alert in the valley ⚠️
Security forces on high alert in Jammu & Kashmir after receiving an input about terrorists are planning su*cidal attack on security force/camps/check post in #Sunderbani, #Nowshera, #Lamberi, #Akhnoor and #Domana of #Rajouri and #Jammu in next 48 hours
👍 1
36722
Фото недоступно
An Anonymous hacker named as Anon-Sanatani Targeting Indian website and putting its demand to kill or take strict action against terrorists..
Threat Actor - ANON SANATANI
https://toshf.in/
https://sapglobalservices.in
https://sapstudyacademy.co.in
https://saptechsolutions.co.in
https://sunapps.co.in
https://omegainstitute.in/
https://indianatvsafety.org/
https://devientrp.in
https://b2o.co.in/
https://adwikanursing.com/
👍 6
360212
Фото недоступно
Bharat ka sona bharat me wapas aa gya
#jaishreeram
#harharmahadev
#UR_DDOS
🔥 3👍 1
3 56845
Выберите другой тариф
Ваш текущий тарифный план позволяет посмотреть аналитику только 5 каналов. Чтобы получить больше, выберите другой план.
